Pentera RansomwareReady™
Explore doc topics
Datasheet
Pentera
Ransomware
Ready™
Answer the Burning Question:
Am I Ransomware Defense Ready?
Am I Ransomware Defense Ready?
Eliminate Ransomware Exposure
Validate ransomware defenses by emulating attacks safely in production, testing security controls, and blocking propagation paths in your network.
Key Product Pillars
-
Complete
Ransomware TestingValidate your security against a wide range of ransomware strains such as REvil, Conti, Maze, LockBit, and more. -
IProof of Ransomware ResilienceSee if your endpoint security can withstand ransomware attacks and if your SOC can detect and respond the way it should.
-
Proactive Exposure IdentificationUnderstand where your defenses are lacking and fix them before they can be exploited by real-world ransomware actors.
-
Clear, Actionable Remediation InsightsCut ransomware kill-chains by remediating vulnerable hosts, deficient controls, and misconfigurations with step-by-step guidance.
1
Datasheet
Ransomware Defense
Validation In-Depth
Pentera safely performs all the actions an adversary would.
Assessment
Identify vulnerabilities, configuration f laws, and security hygiene gaps.
Lateral Movement
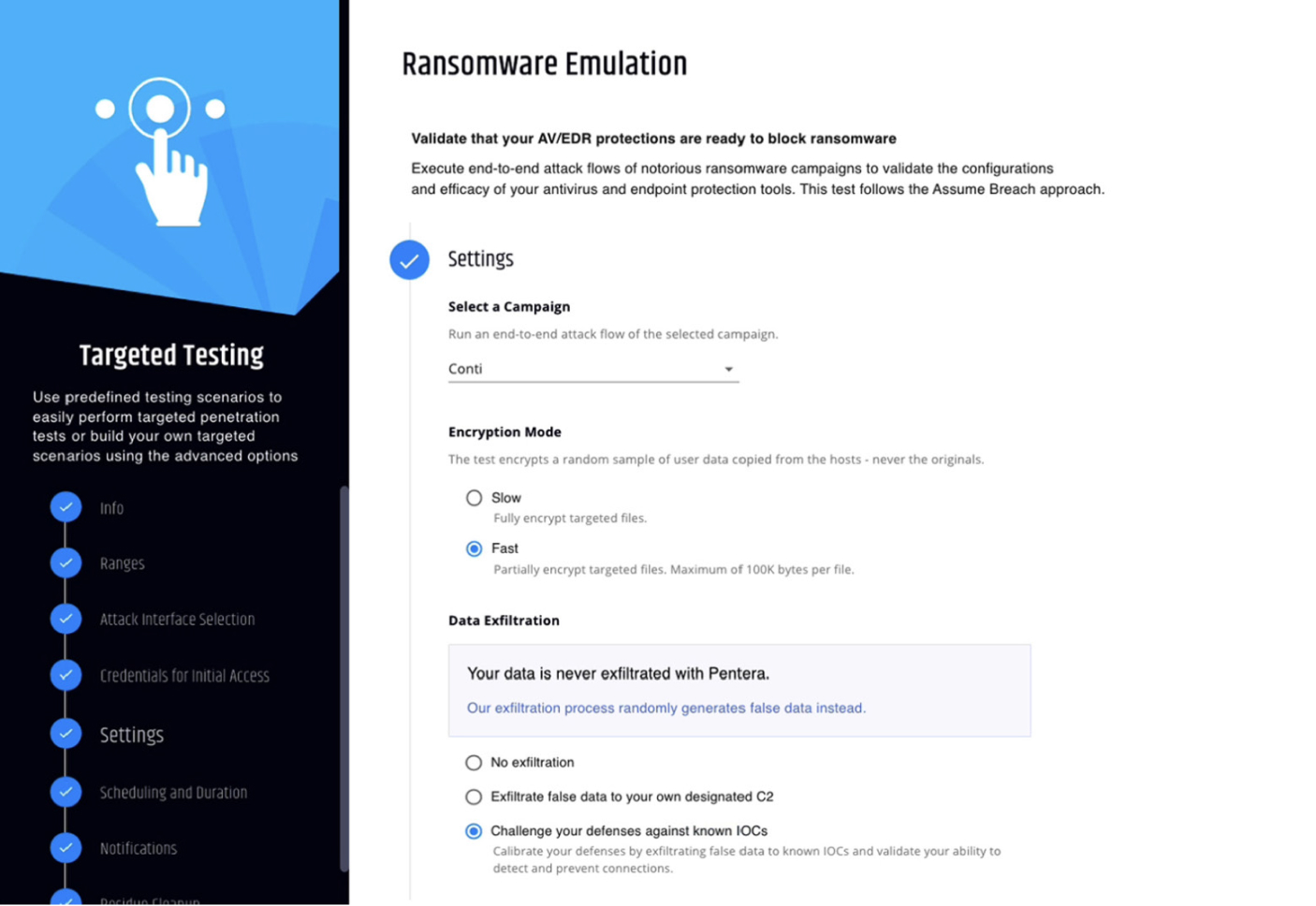
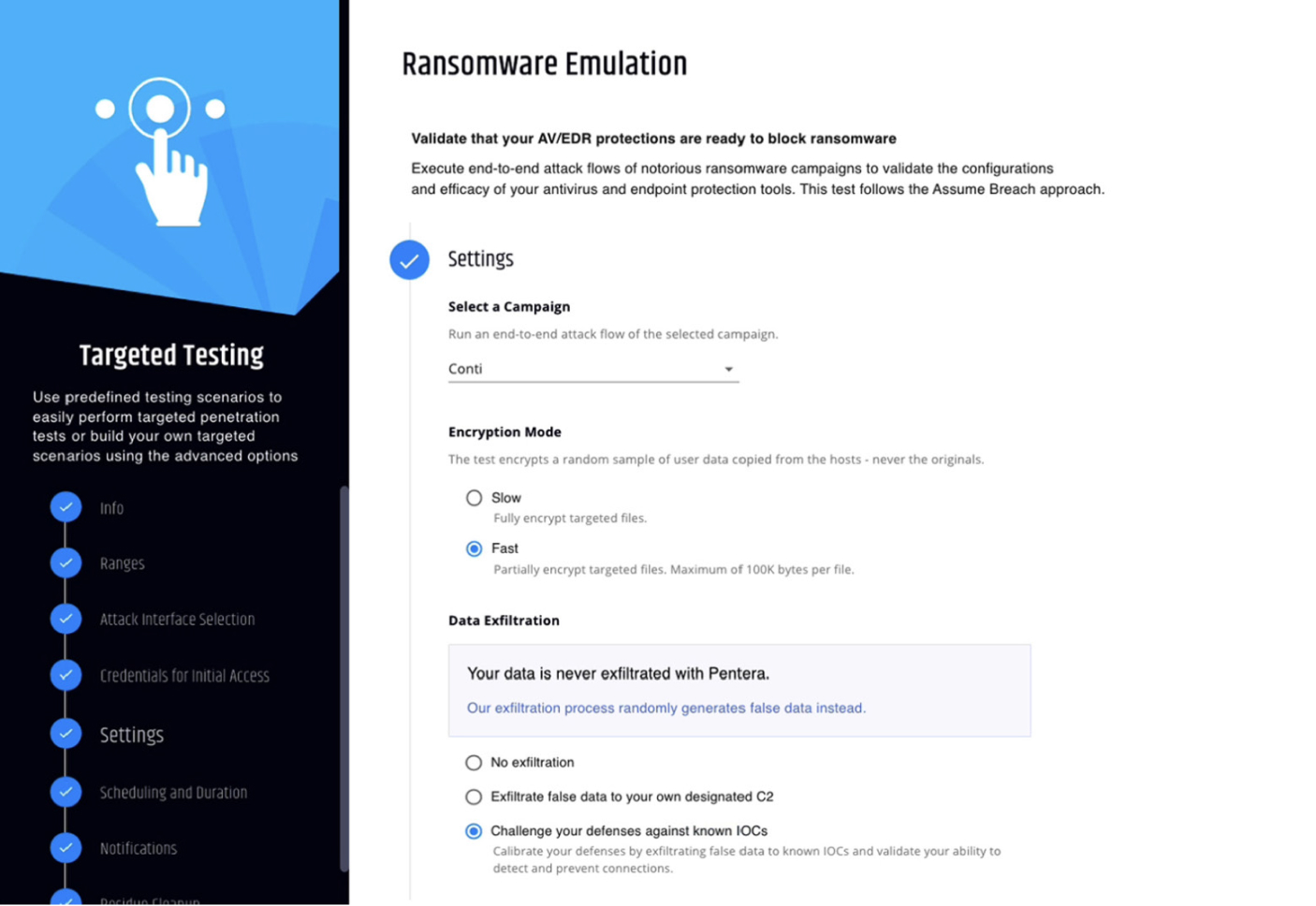
Challenge endpoint protection efficacy with safe malware versions of real ransomware strains.
Safe Encryption
Encrypt a duplicate of existing files.
Cleanup
Clean up the data and code used as part of the test run to leave zero residual footprints.
Reconnaissance
Map the internal attack surface through network discovery and reconnaissance.
Credential Compromise
Use harvested or leaked credentials to advance ransomware attacks.
Exploit Payload
Emulate real ransomware actions such as backup termination and log deletion.
C2 Data Exfiltration
Validate Data Leakage Protection (DLP) systems by connecting to a designated C2 or known IOCs.
Reconnaissance
Map the internal attack surface through network discovery and reconnaissance.
Assessment
Identify vulnerabilities, configuration f laws, and security hygiene gaps.
Credential Compromise
Use harvested or leaked credentials to advance ransomware attacks.
Lateral Movement
Challenge endpoint protection efficacy with safe malware versions of real ransomware strains.
Exploit Payload
Emulate real ransomware actions such as backup termination and log deletion.
Safe Encryption
Encrypt a duplicate of existing files.
C2 Data Exfiltration
Validate Data Leakage Protection (DLP) systems by connecting to a designated C2 or known IOCs.
Cleanup
Clean up the data and code used as part of the test run to leave zero residual footprints.
2
Datasheet
Benefits
-
Reduce ransomware risk exposureProactively build resilience against your biggest cyber threats.
-
Reduce ransomware testing expensesMinimize cost and dependence on third-party ransomware testing services. Leverage automation to emulate attack techniques used by the largest ransomware groups.
-
Increase cybersecurity team efficiencyFocus remediation efforts on proven security gaps to cut ransomware kill-chains.
3
Datasheet
All your attack surfaces, tested continuously
with the Pentera Platform
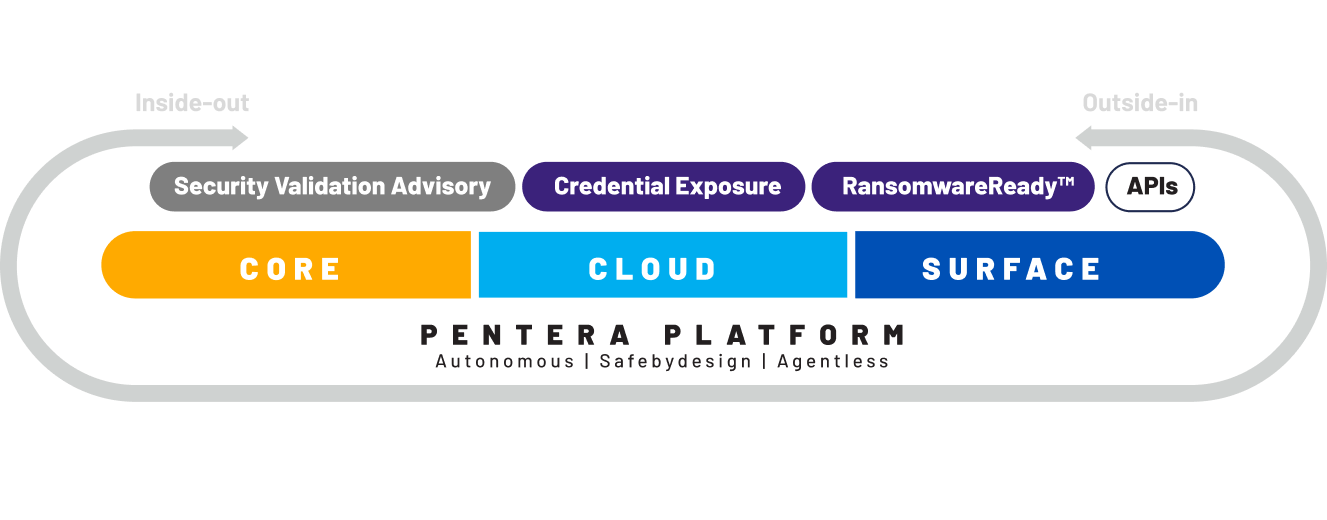
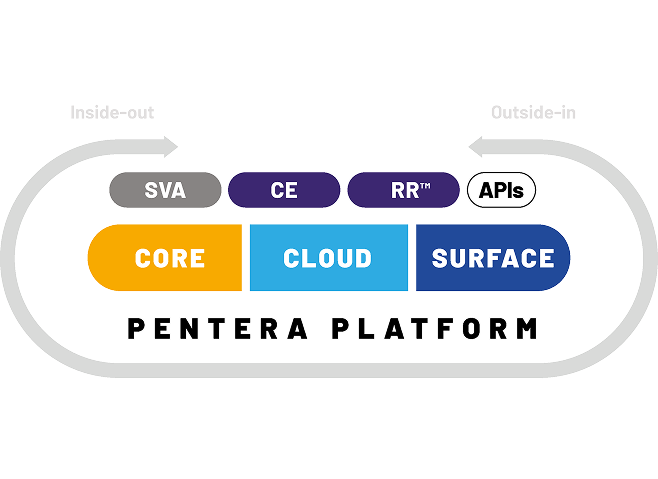
About Pentera
Pentera is the category leader for Automated Security ValidationTM, allowing every organization to test with ease the integrity of all cybersecurity layers, unfolding true, current security exposures at any moment, at any scale. Thousands of security professionals and service providers around the world use Pentera to guide remediation and close security gaps before they are exploited.
4