While phishing and ransomware dominate headlines, another critical risk quietly persists across most enterprises: exposed Git repositories leaking sensitive data. A risk that silently creates shadow access into core systems
Git is the backbone of modern software development, hosting millions of repositories and serving thousands of organizations worldwide. Yet, amid the daily hustle of shipping code, developers may inadvertently leave behind API keys, tokens, or passwords in configuration files, effectively handing attackers the keys to the kingdom.
This isn’t just about poor hygiene; it’s a systemic and growing supply chain risk. As cyber threats become more sophisticated, so do compliance requirements. Security frameworks like NIS2, SOC2, and ISO 27001 now demand proof that software delivery pipelines are hardened and third-party risk is controlled. The message is clear: securing your Git repositories is no longer optional, it’s essential.
Below, we look at the risk profile of exposed credentials and secrets in public and private code repositories, how this attack vector has been used in the past, and what you can do to minimize your exposure.
The Git Repo Threat Landscape
The threat landscape surrounding Git repositories is expanding rapidly, driven by a number of causes:
- Growing complexity of DevOps practices
- Widespread reliance on public version control platforms like GitHub
- Human error and all the misconfigurations that entail: from poorly applied access controls to forgotten test environments pushed to production
It’s no surprise that as development velocity increases, so does the opportunity for attackers to weaponize exposed code repositories. GitHub alone reported over 39 million leaked secrets in 2024—a 67% increase from the year before. These included cloud credentials, API tokens, and SSH keys. Most of these exposures originate from:
- Personal developer accounts
- Abandoned or forked projects
- Misconfigured or unaudited repositories
For attackers, these aren’t just mistakes, they’re entry points. Exposed Git repos offer a direct, low-friction pathway into internal systems and developer environments. What starts as a small oversight can escalate into a full-blown compromise, often without triggering any alerts.
How Do Attackers Leverage Exposed Git Repositories?
Public tools and scanners make it trivial to harvest secrets from exposed Git repositories, and attackers know how to pivot quickly from exposed code to compromised infrastructure.
Once inside a repository, attackers look for:
- Secrets and credentials: API keys, authentication tokens, and passwords. Often hidden in plain sight within config files or commit history.
- Infrastructure intel: Details about Internal systems such as hostnames, IPs, ports, or architectural diagrams.
- Business logic: Source code that can reveal vulnerabilities in authentication, session handling, or API access.
These insights are then weaponized for:
-
Initial access: Attackers use valid credentials to authenticate into:
- Cloud environments — e.g., AWS IAM roles via exposed access keys, Azure Service Principals
- Databases — e.g., MongoDB, PostgreSQL, MySQL using hardcoded connection strings
- SaaS platforms — leveraging API tokens found in config files or commit history
-
Lateral movement: Once inside, attackers pivot further by:
- Enumerating internal APIs using exposed OpenAPI/Swagger specs
- Accessing CI/CD pipelines using leaked tokens from GitHub Actions, GitLab CI, or Jenkins
- Using misconfigured permissions to move across internal services or cloud accounts
-
Persistence and exfiltration: To maintain access and extract data over time, they:
- Create new IAM users or SSH keys to stay embedded
- Deploy malicious Lambda functions or containers to blend in with normal workloads
- Exfiltrate data from S3 buckets, Azure Blob Storage, or logging platforms like CloudWatch and Log Analytics
A single leaked AWS key can expose an entire cloud footprint. A forgotten .git/config file or stale commit may still contain live credentials.
These exposures often bypass traditional perimeter defenses entirely. We’ve seen attackers pivot from exposed Git repositories → to developer laptops → to internal networks. This threat isn’t theoretical, it’s a kill chain we’ve validated in live production environments using Pentera.
High Profile Exposed Git Repo Attacks
Several high-profile security incidents have demonstrated just how damaging exposed Git repositories can be.
- Toyota 2017 to 2022 – In one of the most alarming examples, a piece of source code stored in a public GitHub repository contained an access key to a server that held customer data. This sensitive access key went undetected for five years, ultimately compromising the personal information of over 270,000 Toyota customers.
- Mercedes 2023 – Researchers uncovered a GitHub token belonging to a Mercedes employee in a public repository. Shockingly, this token granted unrestricted access to the company’s internal GitHub Enterprise Service. As a result, proprietary source code across multiple projects was exposed to the public. A major breach of corporate confidentiality and intellectual property.
- Uber 2016 – Uber suffered a breach after attackers accessed a public GitHub repository containing AWS credentials. These credentials enabled unauthorized access to Uber’s AWS infrastructure, where sensitive data of 57 million users and drivers was stolen. Uber paid the attackers $100,000 to delete the data and conceal the breach, a decision that later led to significant legal and reputational consequences.
All of these cases underscore a vital point: that exposed credentials in Git can result in costly outcomes.
Recommended Mitigation Strategies
Reducing exposure risk starts with the basics. While no single control can eliminate Git-based attacks, the following practices help reduce the likelihood of secrets leaking – and limit the impact when they do.
-
Secrets Management
- Store secrets outside your codebase using dedicated secret management solutions like HashiCorp Vault (open source), AWS Secrets Manager, or Azure Key Vault. These tools provide secure storage, fine-grained access control, and audit logging.
- Avoid hardcoding secrets in source files or configuration files. Instead, inject secrets at runtime via environment variables or secure APIs.
- Automate secret rotation to reduce the window of exposure.
-
Code Hygiene
- Enforce strict .gitignore policies to exclude files that may contain sensitive information, such as .env, config.yaml, or credentials.json.
- Integrate scanning tools like Gitleaks, Talisman, and git-secrets into developer workflows and CI/CD pipelines to catch secrets before they’re committed.
-
Access Controls
- Enforce the principle of least privilege across all Git repositories. Developers, CI/CD tools, and third-party integrations should only have the access they need – no more.
- Use short-lived tokens or time-bound credentials wherever possible.
- Enforce multi-factor authentication (MFA) and single sign-on (SSO) on Git platforms.
- Regularly audit user and machine access logs to identify excessive privileges or suspicious behavior.
Where Mitigation Can Get Challenging
Combining these practices will help developers to significantly reduce the likelihood of repository exposures and limit the damage if an incident does occur, but applying them consistently across fast-paced, complex environments is a serious challenge. This is typically where we see things starting to slip up:
Complex Environments and Developer Autonomy
In many organizations, developers have the autonomy to spin up infrastructure or deploy tools without direct security oversight. It’s not uncommon for secrets to be hardcoded “just for testing,” or for misconfigured .gitignore files to be pushed to production.
As organizations scale, tracking where secrets live becomes exponentially harder. Cloud environments, on-prem infrastructure, containers, and even local developer machines each become potential leak sources. Without centralized visibility or controls, secrets can easily become orphaned and forgotten.
Limitations of Detection-only Tools
Tools like GitHub Advanced Security, SAST platforms, and secret scanners play a critical role in surfacing exposed secrets. They flag committed secrets, highlight policy violations, and reduce some of the noise from poor hygiene. But these tools share a fundamental limitation: they detect, alert, but they can’t tell you if:
- Is the secret still active?
- Can it be exploited from the outside?
- Does it grant access to internal systems or sensitive environments?
This lack of exploitability context creates alert fatigue and wastes precious triage cycles, false positives, and introduces remediation uncertainty. Security teams are left unsure where to focus, treating every secret as urgent, without knowing which ones are dangerous.
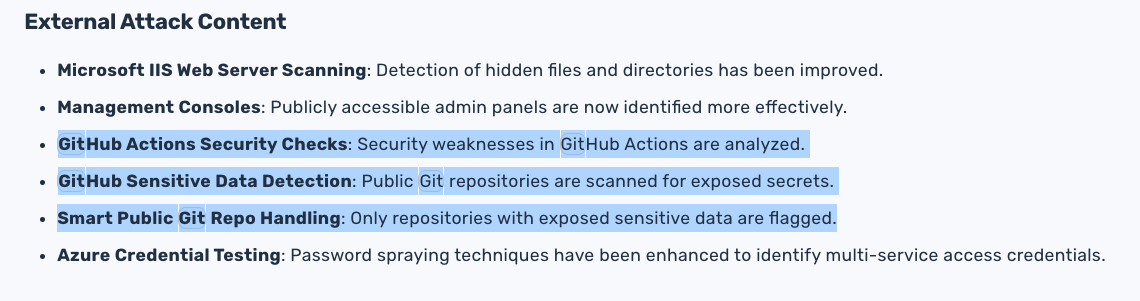
GitHub sensitive data detection (only scanning/alerting for exposed secrets)
Find Exposed Git Data Before Attackers Do
Exposed Git repositories are not an edge-case risk, but a mainstream attack vector especially in fast-moving DevOps environments. While secret scanners and hygiene practices are essential, they often fall short of providing the full picture. Attackers aren’t just reading your code; they’re using it as a map to walk right into your infrastructure.
Even well-meaning teams using best practices are left blind to one critical question: could an attacker actually use this exposure to break in? Securing your repositories requires more than just static checks. It calls for continuous validation, proactive remediation, and an adversary’s mindset. As compliance mandates tighten and attack surfaces expand, organizations must treat code exposure as a core part of their security strategy and not as an afterthought.
To learn more about how your team can do this, view the On-Demand webinar They’re Out to Git You.