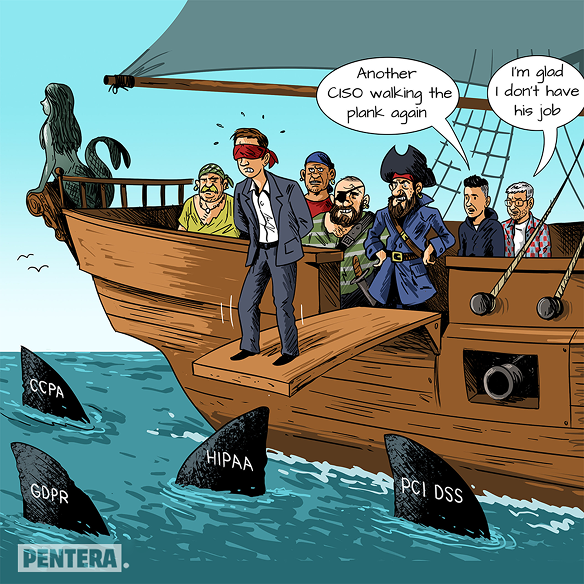
We need to be minded of the job of a CISO as the person who answers for PCI-DSS, HIPAA, CCPA, GDPR, and other regulations in addition to their primary job of making sure the business operation runs securely without too much security and authentication friction. The gap between resources and responsibility is hitting an all-time high for the CISO in the corporate world. A role meant for more than one person, that falls into the lap of one.
Eventually, the CISO’s head is the one on the chopping board in the event of a major breach. Not only do they need to manage the crisis in the round-the-clock warlike dynamics of response and recovery, but in the aftermath, they’re also the ones most likely to be let go. Not fair!