Platform
Pentera Platform
A single platform for everything security validation and remediation
Learn more
AI in Pentera
AI-powered exposure validation
Pentera Labs Research
Advanced research of the latest attack techniques
Integrations
Connect exposure validation with your security ecosystem
Safety & Compliance
Controlled execution with audit proof
Products
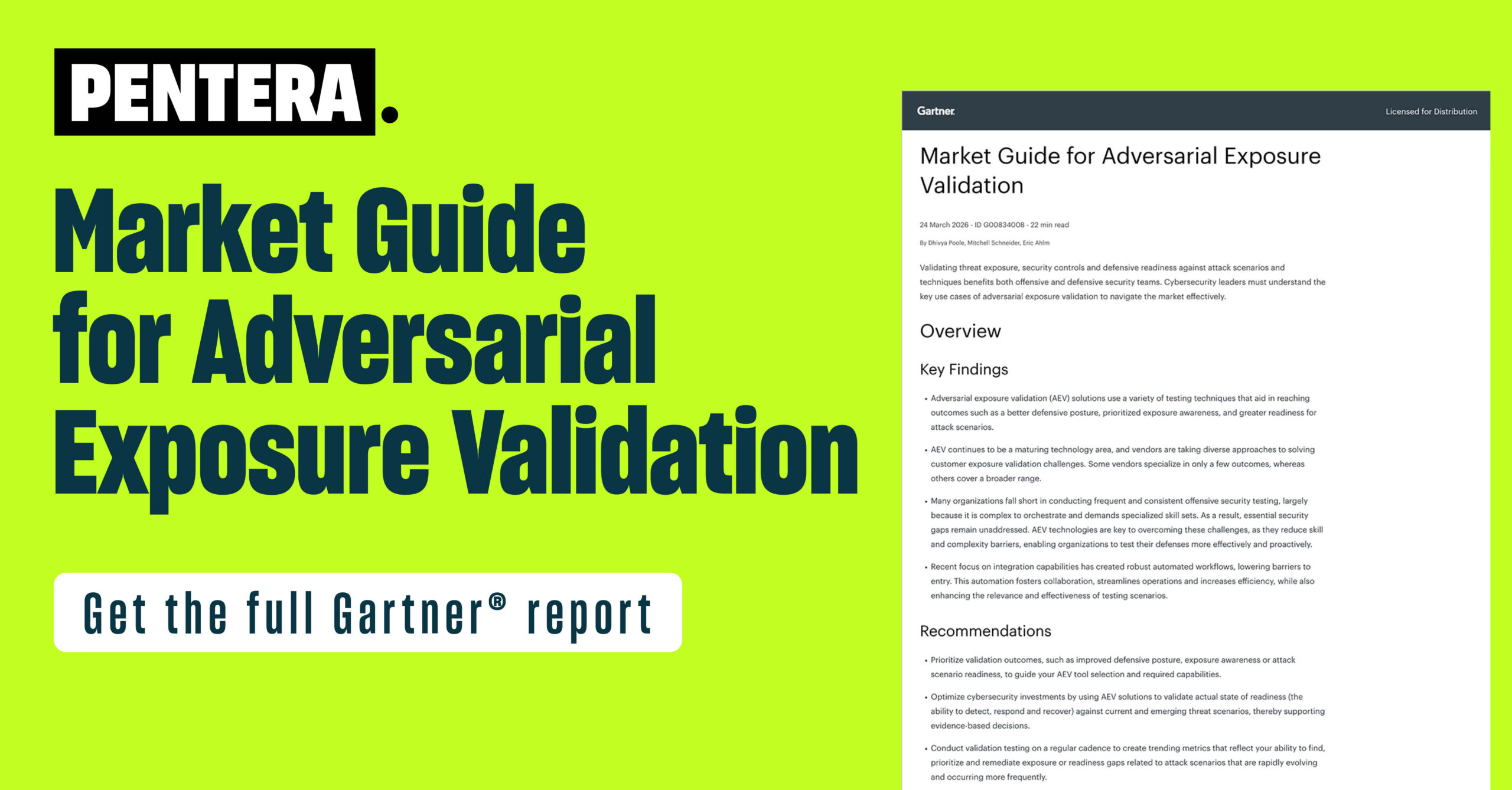
Pentera named a Representative Vendor in Gartner® Market Guide for Adversarial Exposure Validation
Get the report

resources
Feb 2026
LOLBins Against the Machine: Reverse Engineering at Machine Speed
Purpose Attackers can utilize Living Off the Land Binaries (LOLBins) to execute commands, evade detection,...
Read now
Customers

“Pentera helps us prioritize what truly matters and gives us confidence we are covering our global environment continuously.”

“Seeing a domain admin account cracked in production changed how we view internal exposure.”

“Pentera helped us advance our red team and continuously improve penetration testing.”

“Pentera makes it easier to focus on what is truly exploitable instead of chasing long vulnerability lists.”

“In a complex, large-scale environment, Pentera delivers the speed and visibility security teams need.”

“Pentera amplified our team’s performance and delivered measurable value to upper management.”

"Pentera allows us to tailor testing to each service, reduce time and costs, and shift our focus from simply finding vulnerabilities to actively helping our teams fix them.”

Rubén Alonso | Head of Secure
Development Unit, Telefonica
Company
Partners
News & Press
- PlatformPentera PlatformA single platform for everything security validation and remediationLearn moreAI in PenteraAI-powered exposure validationPentera Labs ResearchAdvanced research of the latest attack techniquesIntegrationsConnect exposure validation with your security ecosystemSafety & ComplianceControlled execution with audit proof
- CompanyAbout PenteraLearn who are we and what’s our missionCareersOpen roles across engineering, research, and go-to-marketTrust CenterSecurity, privacy, compliance, and certificationsContact UsWrite to us and we’ll get back to youPartnersBecome a PartnerBecome a Pentera partnerPartner ProgramLearn how we support our partners across the globePartner LoginAccess the partner portalNews & PressNewsroomCompany announcements and press releases



