Much of a company’s assets are connected to Wi-Fi networks. However, security teams are often less likely to validate these networks. This pushed us to wonder what we might find if we were to test a corporate WiFi network.
After running the Pentera platform™️ over Wi-Fi, we found several vulnerabilities, which helped us gain insight into potential security gaps in these networks.
Most security teams prioritize physically connected segments and static environments when assessing the attack surface. Often, devices and PCs connected to Wi-Fi and other radio networks, including guest devices, IoTs, and employees’ mobile phones, tablets, or laptops, are only validated and secured afterward.
That’s why most penetration testing assessments start from a port in the wall and an ethernet cable and is also how a Pentera machine will be connected to an enterprise’s network.
Correspondingly, as part of continuous validation, we connected a Pentera machine to a corporate’s public and private Wi-Fi networks. This test took place over an extended period to cover both daily work hours and night when offices typically stand empty.
The Detailed Tale
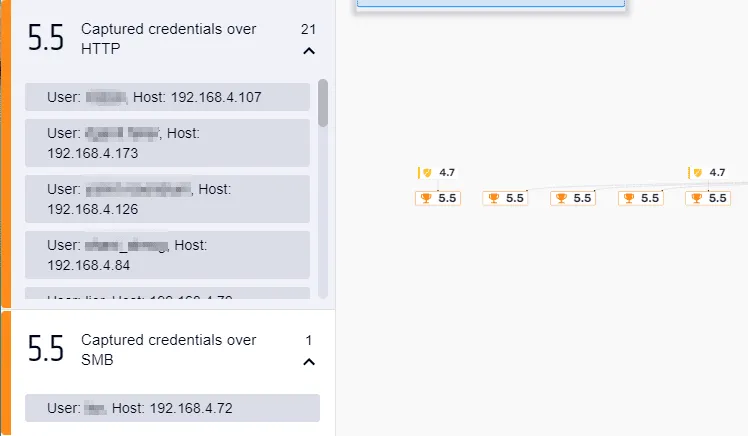
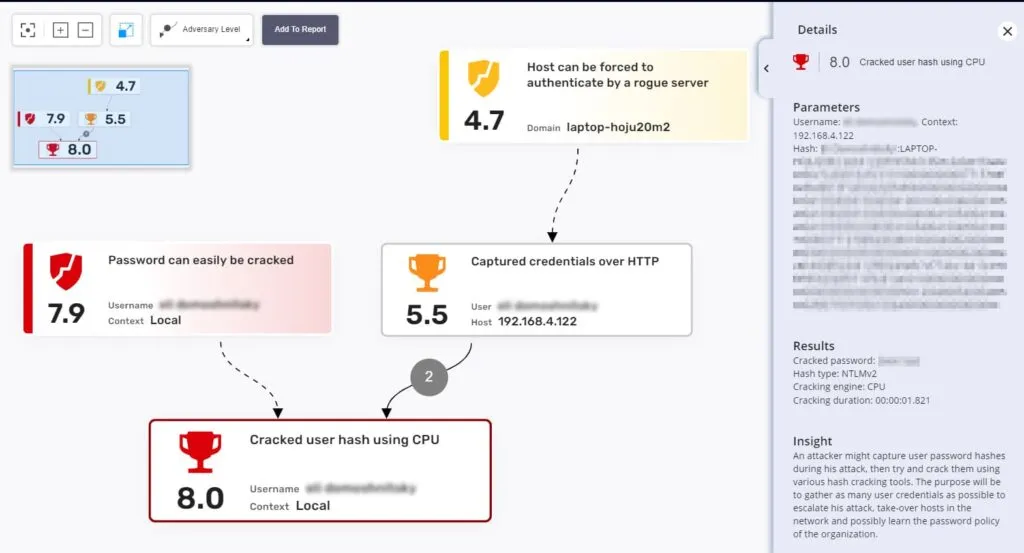
During the day, we were able to obtain multiple achievements, such as Sniffed Credentials over various protocols caused by company employees who were connected to the office Wi-Fi network.
At night, when we didn’t think we’d achieve any results is when multiple key events occurred.
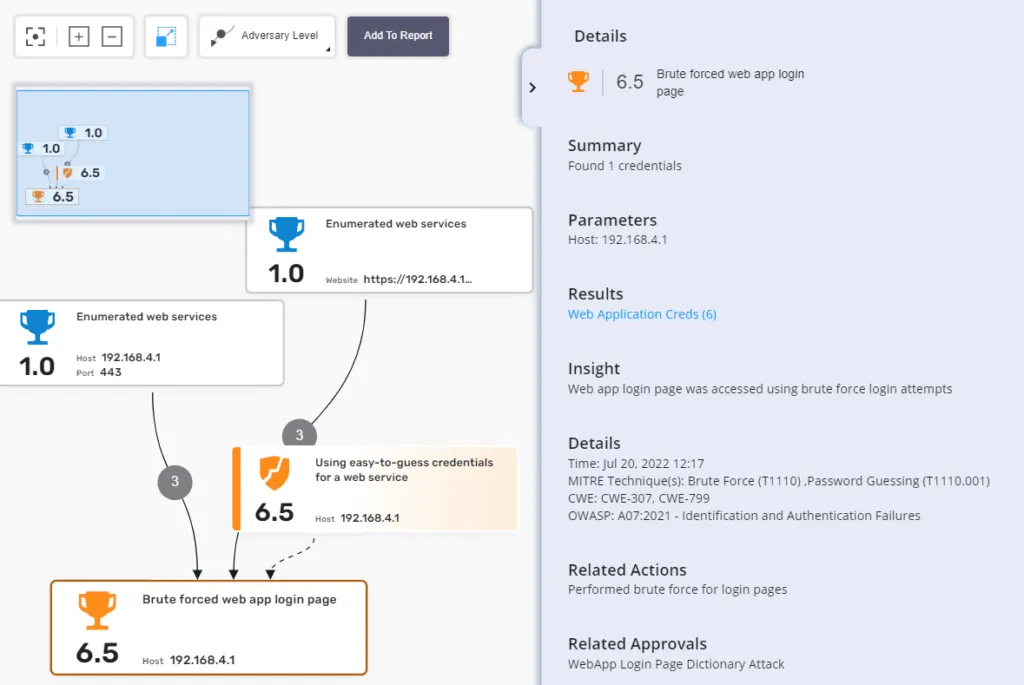
The Pentera Platform™️ was able to discover and enumerate multiple web applications reachable over the Wi-Fi network.
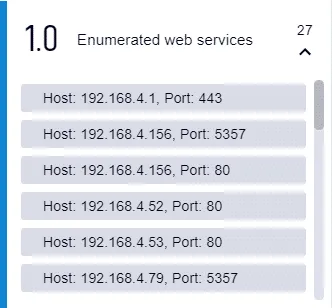
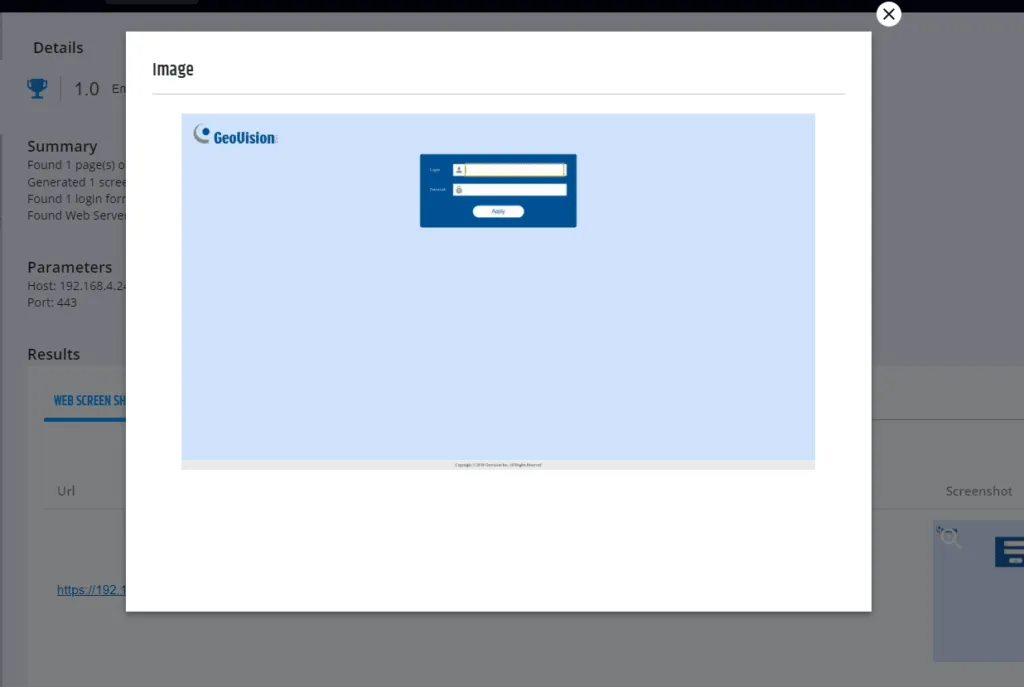
Among the 20+ applications discovered and mapped was the management interface of the office cameras and alarm systems.
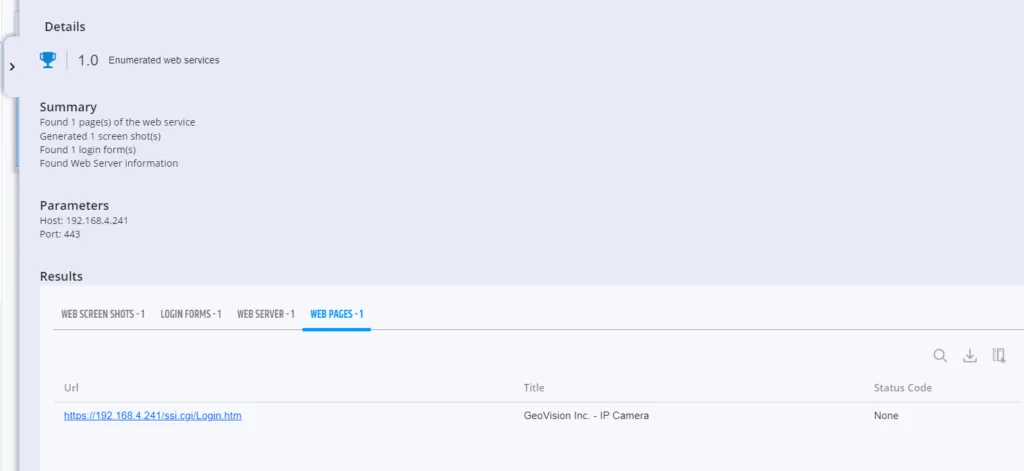
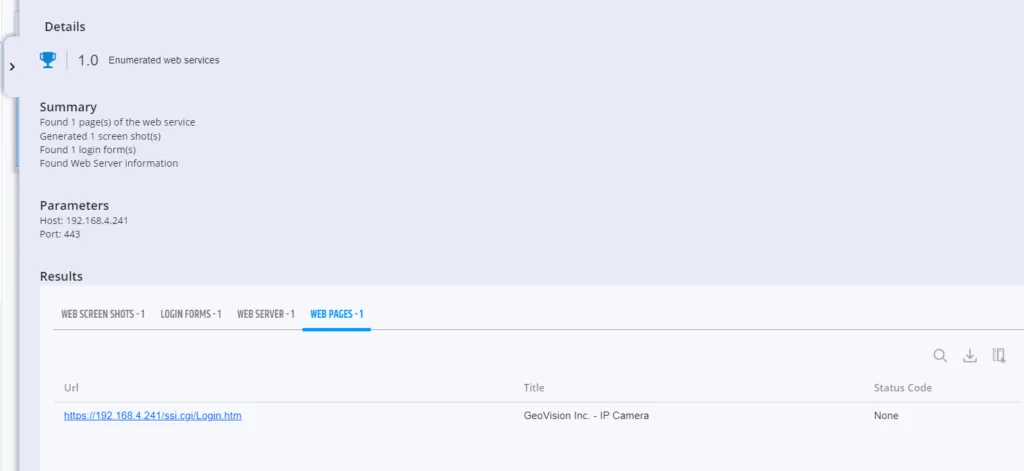
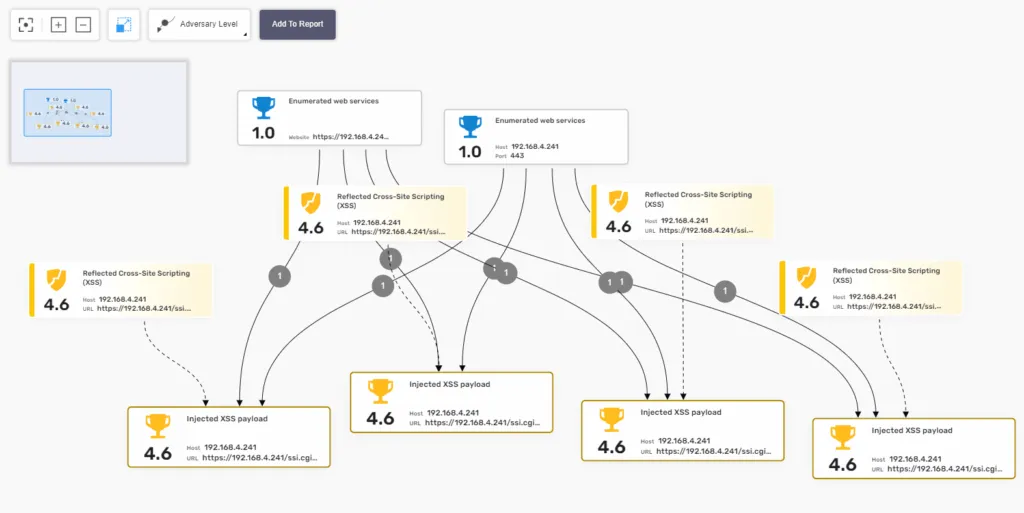
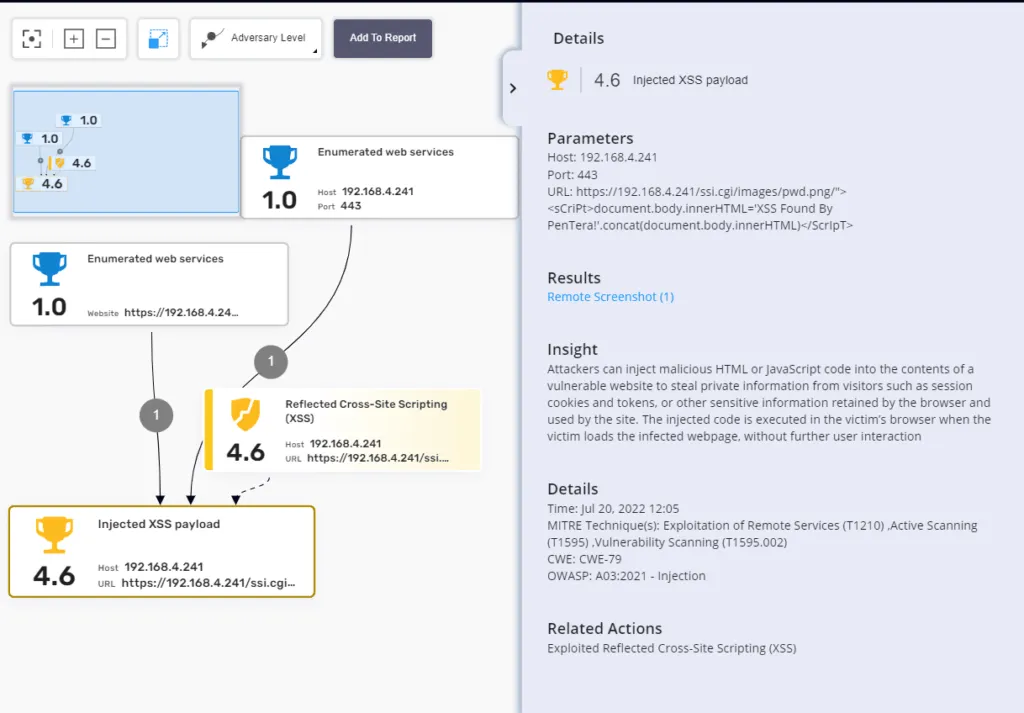
Multiple XSS vulnerabilities were detected on the cameras’ management platform interface. An example is provided in the screenshot below.
Pentera was able to brute-force the credential to the admin interface of one of the switches.
At roughly 3:00 AM, Pentera started fuzzing the security systems, causing the alarms to go off, which prompted the security and office manager to respond. The event was dismissed as a false positive. It wasn’t until the next morning that the real impact of the test was realized.
In addition to traditional key locks, the main office door and other important internal rooms have electromagnetic locks that can only be opened with a combination of specially encoded access cards. However, in the morning, when employees started arriving at the office, they could not enter. All magnetic doors were locked and could not be opened in any way. Having suspected that this may be the effect of Pentera fuzzers and stacks on the controllers of the door mechanisms, we opted to conduct further testing under lab conditions in a more controlled environment. Once again, we were able to cause all controllers to go dark, effectively locking access to the offices.
Now, imagine how your employees would have reacted if this would have happened at your organization. Even worse, what would a real malicious attacker have done with this? I doubt they would call to apologize and stop their activity with a screenshot.
Jokes aside, the moral of this story is that often the places we explore and test the least, are the most exposed and prone to intrusions.
Stay secure with continuous security validation
If you’re a current Pentera customer, we highly recommend that you start running tests on your own Wi-Fi and IoT networks. For everyone else, we invite you to reach out to us for a free test on your own environment.



























