22 Feb 2023
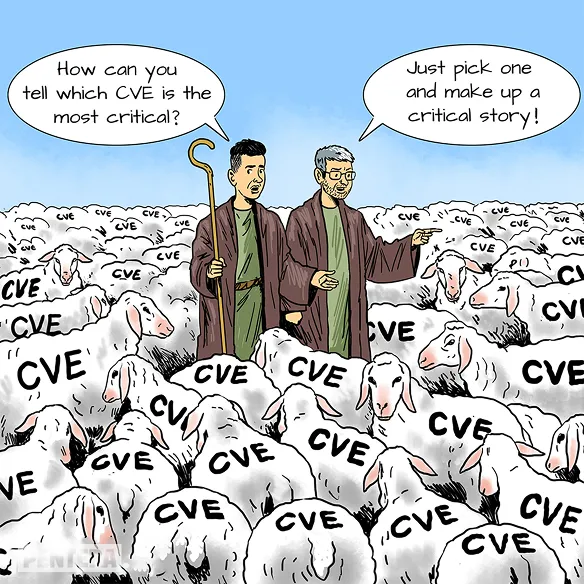
CVSS – One Size Fits None









Rubén Alonso | Head of Secure
Development Unit, Telefonica