A lot of respect and appreciation is due to today’s medical staff, there’s no doubt. But I would argue that we owe just as much to the cybersecurity teams keeping our businesses, economy, and in a sense, our livelihood, protected.
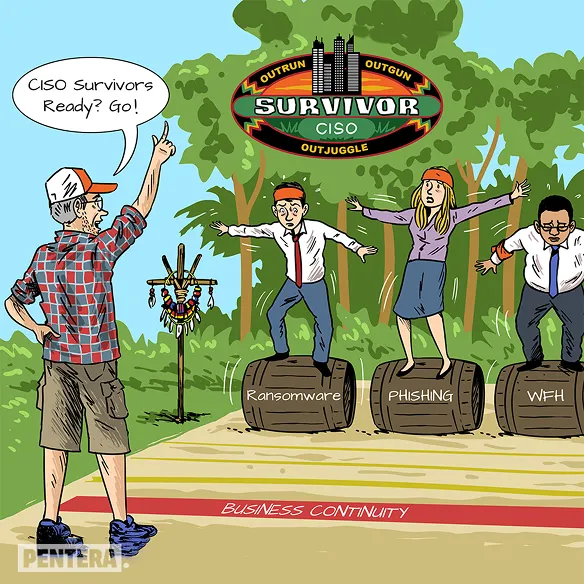
I call them Corporate Patriots™ – and they deserve our appreciation, gratitude, and respect during these hard times. The CISO’s role is one of the most difficult ones in the world. It’s a job for survivors.
During these pandemic days, the gap between the CISOs’ tasks and the means they have to perform them is reaching an all-time high. More attacks and more attack surfaces, with less budget and less staff. When you pile on the WFH challenges, I believe we can agree that this Cybertoon is actually an understatement of their realities.