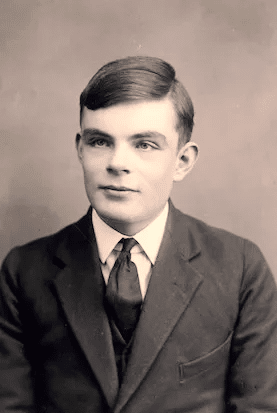
Computer-room heroism or what I like to refer to as “Cyber Patriotism” is told in the compelling story of The Imitation Game. Based on the book “The Enigma” by Andrew Hodges, the film tells the story of crafting the first computing machine to decipher the Nazi Enigma code. It is also the story of Alan Turing, the English computer scientist who formalized the concepts of algorithm and computation with his Turing machine and mathematical model of computation.
Today, the cybersecurity space is reliving this story. The bad guys seem to have the upper hand. The malicious hackers, organized crime hackers, nation-sponsored hackers, hacktivists, and wannabes are all after the corporate cyber vulnerabilities.
But if you take a wide angle view of the global cyber warfare picture, you will see a grave asymmetry parallel to The Imitation Game. In today’s cybersecurity world, there is asymmetry in favor of the computerized aggressor vs. the security defender drowning in manual labor. While all cyber analysts will agree that cyber defense automation must be the next step, CISOs are struggling to achieve it.
For example, the most effective and accepted way of validating your entire array of cybersecurity defenses is penetration testing. This service often performed annually, is done manually. On the other end of the cyber frontier, hackers are using computerized power to launch attacks on every virtual “square inch” of the corporate IT attack surface 24/7. It’s a man vs. machine battle. We simply cannot win in the same way the UK team could not decipher the Enigma code within 24 hours, no matter how many people tried.
The solution can come only in the form of a machine, which can imitate a hacker using computer power to validate the corporate defenses, not just once a year, but 24/7. Making sure that your guard is consistently up and pointing to remediation required in small daily doses rather than once a year is key.
The solution to winning in cyber warfare requires a machine that advances it’s testing to keep pace with the new exploits and hacking methods. It is not based on dated “playbooks” of one’s town consulting firm who struggle to keep up their research and penetration testing tools.
The Imitation Game had a happy ending. All we need to do is automate our cyber defense validation practices to have one too.





























