Pentera Surface
Pinpoint true web-facing
security gaps.
Harden your external attack surface.
External security validation in-depth.
Discover how our platform
can make a difference for
your security.
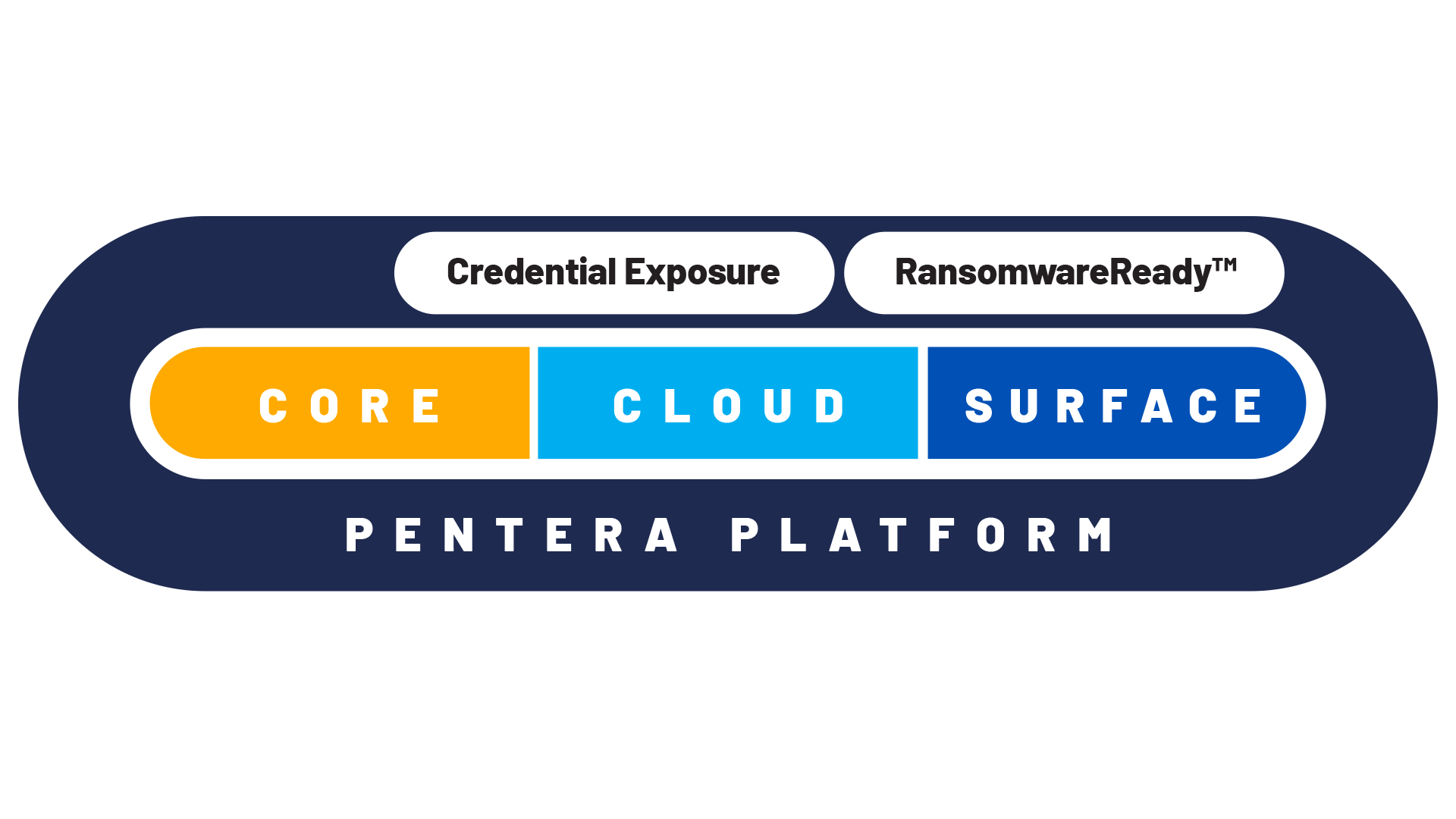
Validate your entire attack
surface with the Pentera
Platform.
Fix the security gaps that really matter.
Helpful resources for smarter security validation.
FAQ
How does Pentera Surface discover assets?
With only a single domain provided, Pentera will discover associated domains, subdomains, IPs, networks, services, websites, and external code repositories. The discovery is done automatically, if an asset is not owned by the customer, the customer can decline the ownership, and it will automatically be removed from the account. Pentera has a confidence algorithm that makes sure that each asset is associated with the customer. If an asset does not have a high confidence level, it will not be validated by Pentera Surface.
What do you need to provide to Pentera in order to start the Surface discovery?
To start a Pentera Surface discovery, you only need to provide the organization’s external-facing identifiers such as domain names, IP ranges, or URLs, that you want tested. From there, Pentera automatically enumerates exposed assets, maps the external attack surface, and validates which exposures are exploitable. No agents, credentials, or special configurations are required.
How is customer data protected in Pentera Surface?
We are in the process of certifying Pentera Surface with SOC 2 type II, covering the following trust service principles: Security, Confidentiality, and Privacy. It means that all data is encrypted, authorizations are properly enforced, and that control mechanisms and authentication are at enterprise grade.
Can Pentera Surface replace our external penetration testing?
Yes, Pentera Surface discovers shadow assets, exploits misconfigurations, and maps full attack paths, providing deeper, repeatable insights than point-in-time external pentests. Many organizations reduce their dependence on external pentests, thereby cutting costs while gaining continuous visibility. For compliance that mandates manual testing, an attestation will still be required, but Pentera can complement this process by ensuring auditors focus only on validated, exploitable risks.
Can Pentera Surface replace our EASM (External Attack Surface Management)?
Yes, Pentera Surface offers the same capabilities of EASM and goes further. While EASM tools focus on continuous discovery and inventory of internet-facing assets, Pentera Surface validates which of those assets and exposures can actually be exploited.
Are users able to control advanced exploitations in Pentera Surface?
Pentera Surface automatically performs pentesting, however advanced actions, like web vulnerabilities that leverage remote code execution, needs to get prior approval according to the user policy.