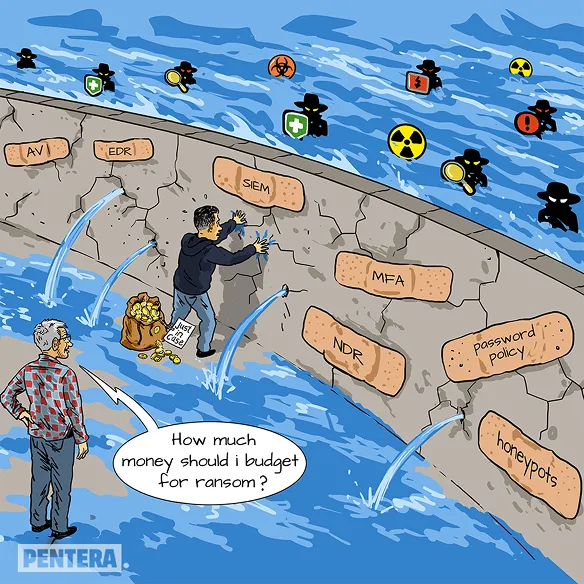
Hans Brinker may have saved Holland by plugging his finger in a hole, but we know that’s not sustainable, not scalable, and doesn’t work in practice – certainly not in cybersecurity. We add more tools to our security tech stack, hoping we’re covered. While it may feel like you’re “dammed” if you do, damned if you don’t, ransomware is not an inevitability.
Instead of relying only on our defenses which we know can and will be penetrated, we need proactive visibility and better control. Frequent testing helps us understand where weaknesses may become cracks and which cracks may spring a leak, so we can focus the right resources in the right places. With the right prioritization of remediation to allow for a fix instead of waiting to cover the wound with a band-aid, you are better equipped for ransomware.